Data protection and security needs have been evolving, especially with remote working, growing frontline employees and rapid adoption of BYOD and a perimeter-less working culture. Windows laptops and desktops enjoy huge popularity in the enterprise as well as personal usage space.
The security of corporate data on the BYO PCs (employee-owned Windows computers and laptops) is in jeopardy when these devices operate outside the corporate networks and infrastructure.
This is where the Microsoft Windows Information Protection Policy comes to play in securing corporate data.

In this article, let us have a deep insight into Windows Information Protection- WIP for Enterprise Data Protection.
What is Microsoft Windows Information Protection (WIP)?
Windows Information Protection is a set of policies that help organizations and their subsequent IT teams in securing corporate data on primarily employee-owned devices without hampering the overall user experience, which is the prime reason for heavy Windows adoption in the enterprise environment.
The Microsoft Windows Information Protection (WIP), previously named Enterprise Data Protection (EDP) was introduced along with the Windows 10 anniversary update in an effort to support and complement the Windows 10 modern management.
When we define Windows Information Protection or WIP meaning, it is most often affiliated with employee-owned Windows desktops and laptops.
But it is important to understand that Windows is an ownership-agnostic operating system, which means that Windows Information Protection (WIP) can be also used to secure corporate data on 100% corporate-owned, fully-managed devices.
Why Use WIP – Windows Information Protection?
The number of personal Windows devices used for business is exponentially increasing. While some organizations rely completely on the employees using their personal devices for work, many allow and depend on partial usage of employees’ devices- it could be to complete a task on a weekend, address an emergency or while working remotely.
The increased proliferation of employee-owned devices in the workplace (on-prem or remote) has resulted in added concerns around corporate data security.
The increasing risk of data being leaked accidentally via one of many websites or apps the employees access on their personal computers is the primary reason why enterprises need WIP.
It also secures the corporate data against intentional breaches attempted by the employees while accessing corporate data on the device where they also have access to social media, sharing and public cloud storage.
The advantage of the WIP policy is that it doesn’t overtake or overlap with the user experience of the computer. Unlike a fully-managed device controlled using an enterprise mobility management tool where IT admins block/restrict access to non-business and unauthorized apps, the Windows Information Protection policy works in sync with the employees’ control and privacy while their personal devices.
What are the benefits of Windows Information Protection (WIP)?
- Protecting corporate data on employee devices
- Ensuring no changes to the existing enterprise environment and apps
- Facilitate the original Windows user experience

Enterprise Data Protection using Windows Information Protection (WIP)
The primary idea of WIP is to not only protect the corporate data on the employee devices but also to bifurcate the corporate data and the personal data on the employee devices and selectively apply data protection policies for the corporate data.
This ensures that while the corporate data is protected upholding the enterprise’s security posture, the employee’s personal data is unimpacted.
Let us see how WIP impacts:
Corporate Data
WIP adds a corporate tag or identity to the corporate data on the employee devices and automatically encrypts the data when it is downloaded, saved, or obtained from the pre-defined corporate sources.
These sources include corporate apps, corporate networks, and protected corporate domains. Any data flowing in from these sources is encrypted using WIP.
IT administrators can define the WIP policy and prevent copying of the corporate data and pasting it in the personal apps/data. The corporate data files can only be accessed via protected apps and cannot be accessed from unprotected apps.
Personal Data
Personal data of the employee remains undeterred and unimpacted with the application of the Windows Information Protection (WIP) policy.
When the organizations disable the WIP policy on the retired devices or devices of employees that are no longer associated with the organization, the personal data remains as is.
Even when a Windows device remote wipe is performed using an MDM, the personal data remains intact. This is one of the key advantages of Windows Information Protection (WIP).
Enlightened applications Vs Unenlightened applications
We need to understand the two basic types of apps and their terminology used in accordance with Windows Information Protection. The two types of commonly referred apps with respect to WIP are- Enlightened applications and Unenlightened applications.
Enlightened Apps:
These are the apps that can differentiate between corporate data and personal data. Microsoft Office 365 ProPlus apps such as MS Word, MS Excel, MS PowerPoint, MS OneNote, and MSOutlook are enlightened apps.
Unenlightened Apps:
These are the apps that cannot differentiate between corporate data and personal data. Common examples of unenlightened apps are Gmail and Google Chrome Browser.
While the IT admins create WIP policy they choose unenlightened apps as allowed apps, corporate data can be accessed via these apps. The unenlightened apps treat all the data on the device as corporate data and encrypt it.
This also includes an employee’s personal data. The Windows Information Protection (WIP) policy ensures that when an unenlightened app is necessary for business operation, the data is always encrypted.
It is recommended to allow only enlightened apps while the WIP settings ensure that only corporate data is encrypted. This resolves the common concern around how to protect client information on windows 10 or how to protect confidential information in windows.
Managed Apps:
These are the apps running on the devices in the enterprise context. These are not personal apps enabled by the employee and have to be allowed by the IT admins. These apps are also known as corporate apps or enterprise apps.
Windows Information Protection Use-Case
The most common use-case of Windows Information Protection is for BYOD devices. For instance, a user has access to several enterprise documents and images.
On the same PC, she/he can upload the enterprise document to their personal cloud storage or share it using social media without Windows Information Protection (WIP).
Or the employees can share any sensitive business information over their personal email, inviting data attackers. Similarly, users can open a personal file using an enterprise application.
Setting up WIP for Windows 10 Devices using Scalefusion MDM
In this section, we will learn how to configure WIP step by step on Scalefusion Windows 10 MDM. but let’s start with the Windows Information Protection requirements.
Windows Information Protection (WIP) Prerequisites
- Windows 10, version 1607 and later
- Windows 10 Mobile, version 1607 and later
- Scalefusion MDM solution for WIP setup
Step-by-Step Guide for WIP setup
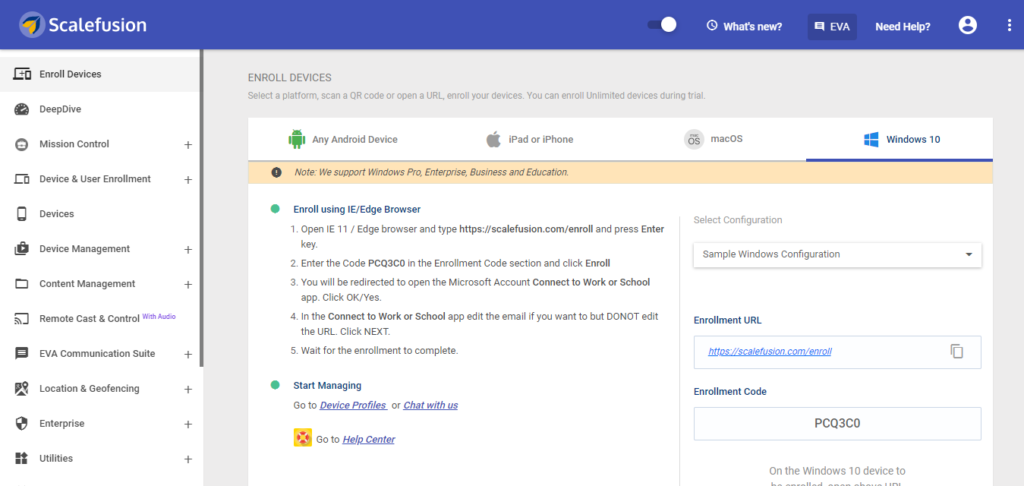
Step 1: Get Started on Scalefusion
To enable WIP on Windows 10 devices, signup and login on to the Scalefusion MDM platform. You can use your corporate ID to sign up or sign up using Azure AD credentials to further leverage the Azure AD-joined settings.
Signing up using Azure AD while also helping you to seamlessly add users to the MDM dashboard and send them an invite to enroll their BYO devices into management.
Once you have enrolled the devices into the MDM platform, you can start configuring usage policies of the Windows 10 devices for work.
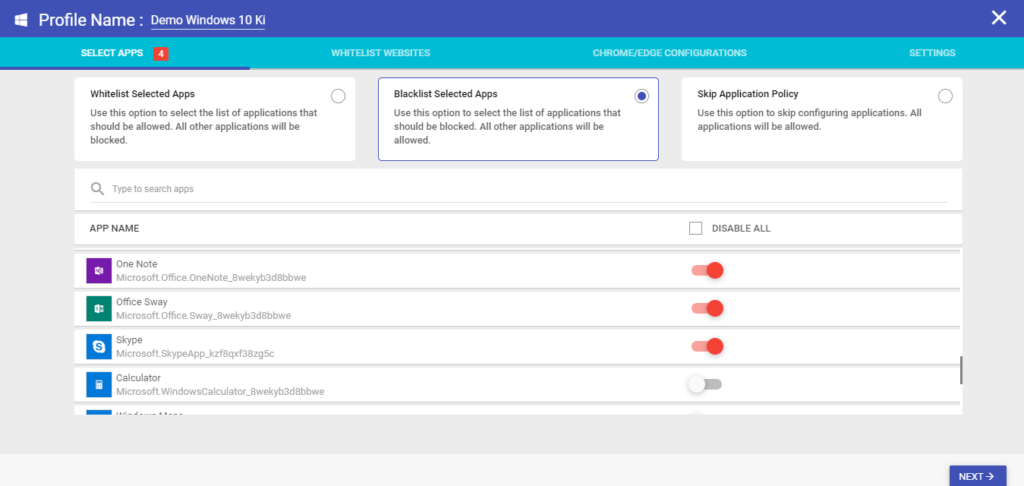
Step 2: Defining Device Profile/Policy
Navigate to the Device Management section of the dashboard. Create a profile or edit the existing device profile that is to be applied to the BYO PCs. Enables apps and whitelist websites to be accessed on the device.
Step 3: Create a Windows Information Protection (WIP) policy
In the settings section, you can activate Windows Information Protection. If you skip the settings, you cannot enforce it on the BYOD devices. Let us have a look at the detailed settings available for enabling WIP mode.
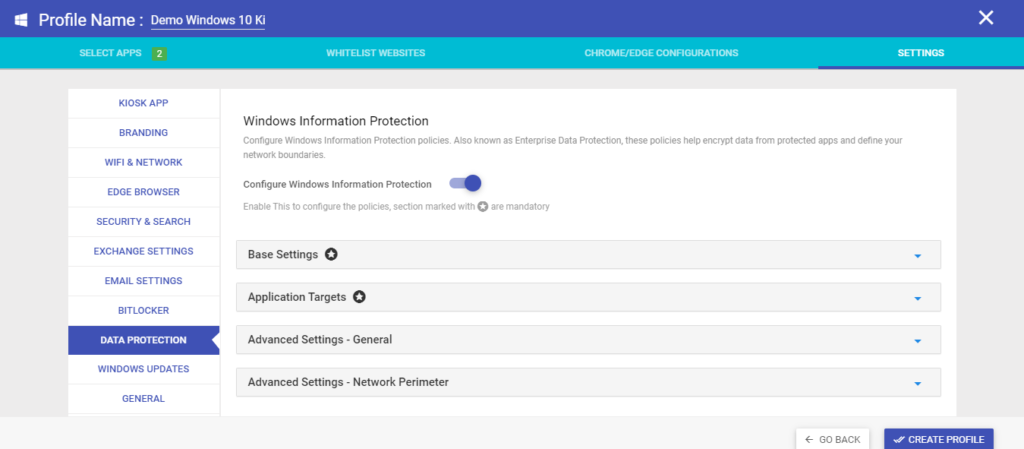
- Base Settings
Configuring these settings is mandatory.
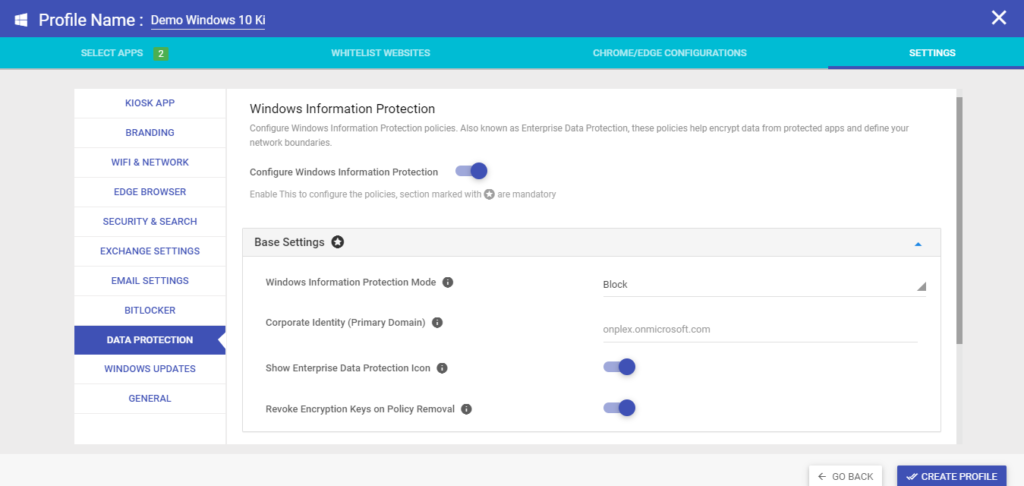
1.1 You can select the protection level of the Windows Information Protection mode.
- When you turn it off, data copy is allowed between managed and unmanaged apps.
- In the Allow and log actions setting, the copy actions are logged. These data can be obtained from the WIP audit logs
- In the Allow Overrides & Log Action setting, users are simply shown a warning while copying the data and the user can override the settings.
- For full protection of corporate data, it is recommended to select block setting, which prevents any copy of data between protected and unprotected apps.
1.2 Define the corporate identity which is the primary domain- the data in motion from this domain will always be encrypted with the help of Windows-provided Encrypting File System (EFS).
1.3 You can choose to hide or display the WIP briefcase icon which will appear on protected apps and data files. If the employees need to know how to check if Windows Information Protection is enabled for a particular file/app, they can check the briefcase icon on the top right corner.
1.4 Enabling this setting will make the corporate data files readable when the IP is disabled from the devices or the devices are no longer enrolled into Scalefusion MDM.
- Application Target Settings:
These are also mandatory settings.
2.1 Here, select the UWP or Win32 apps that are allowed access to the enterprise data. Choose the data from which apps are protected and which apps are exempted. You have to at least select one application. For example, if you want to enable WIP for Chrome browser, you can select the Chrome Browser from the list of apps.
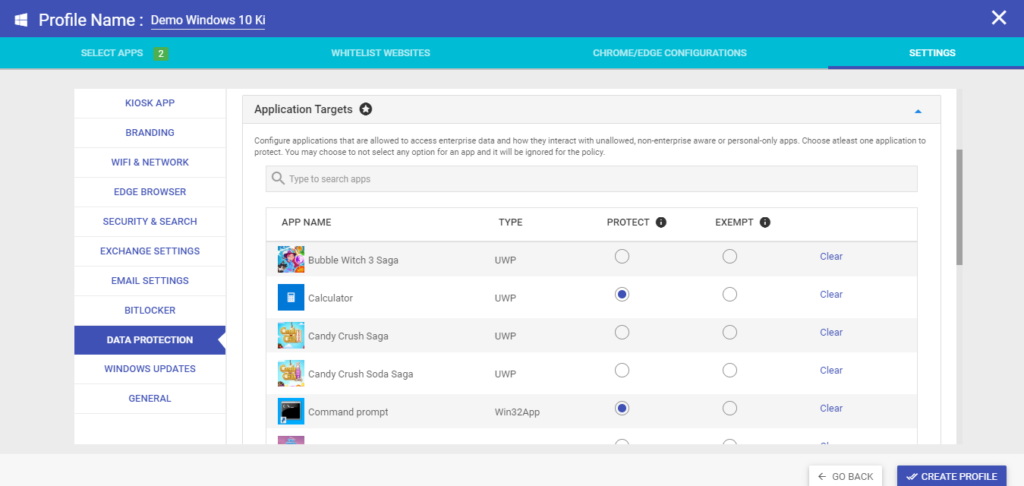
2.2 If you select the protect option for any app, the app will be able to access the enterprise data while honouring the auto-encryption/tagging policies. The data in motion from these apps, files downloaded from these apps will be encrypted on the disk.
2.3 The exempt option is suited for apps that are not compatible with WIP but still need to have access to the enterprise data. If you select this option, the app will have access to the corporate data but the data will not be encrypted and can cause leaks.
We recommend protecting all apps for the security of corporate data. If any of the apps are not able to handle the corporate data files, we recommend selecting the exempt settings instead of clear.
- Advanced Settings: General
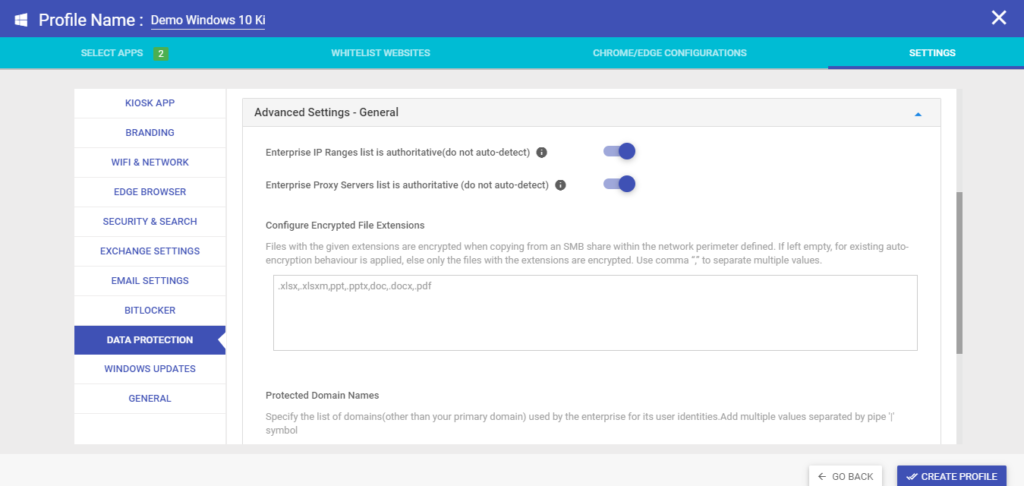
3.1 Enterprise Proxy Servers list is authoritative (do not auto-detect): If you enable this setting, users can override Windows auto-detection of proxy servers.
3.2 Enterprise IP Ranges list is authoritative (do not auto-detect: After enabling this setting, users can override Windows auto-detection of IP ranges.
3.3 Encrypted File Extensions: Define the file extensions that have to always be encrypted. If no file extensions are defined, auto-encryption will be enabled. You can add multiple file extension types using a comma.
For example, if you do not have to encrypt any video file type on the device, it will always be exempted from encryption.
3.4 Protected Domain Names: Select and add the list of domains other than your primary domain for which encryption will be automated. This can be your email domains etc. You can add multiple domains separated by the pipe symbol.
- Advanced Settings: Network Perimeter
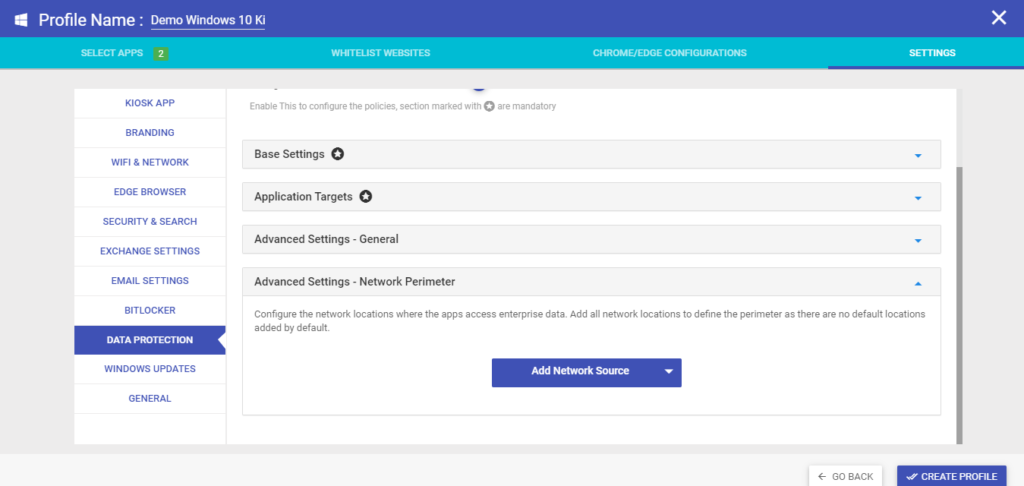
Choose where the protected apps can access enterprise data. Select the enterprise network location, add network sources for encryption. For remote working employees, it is recommended to specify all network sources. The Windows Information Protection blocks internet connections that are not identifiable from accessing enterprise data via these settings.
4.1 Enterprise Cloud Resources: Select the cloud resources that are to be treated as protected.
4.2 Enterprise Protected Domains: Select the DNS names forming your enterprise network. This will help in defining the network perimeter along with the IP ranges.
4.3 Enterprise IP Ranges: Add the IP ranges for the enterprise network. You can add multiple values.
4.4 Internal Proxy Servers: Specify the proxy using which the traffic to the enterprise cloud is to be routed.
4.5 External Proxy Servers: Add the list of your external proxy servers through which the traffic is to be allowed and protected.
4.6 Neutral Sources: Add the authenticated redirection endpoints for your enterprise.
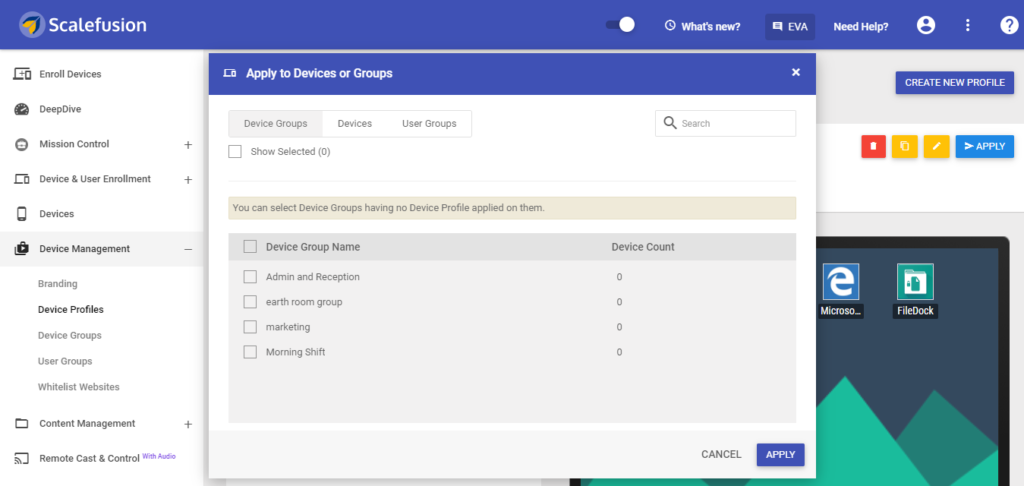
Step 4: Update profile
Save the profile settings and apply them to the device. All the devices with this policy will now be enabled with these settings for WIP. You can apply the profile to a device or a device group.
If you want to know how to check Windows Information Protection status, you can simply visit the profile on the Scalefusion Dashboard and see which profiles have it enabled.
Limitations of Windows Information Protection (WIP)
Weighing the Pros and Cons of Windows Information Protection (WIP) is important before configuring the settings on an enterprise level. Although WIP is one of the key data security features offered by Windows 10, there are a few limitations of WIP such as:
- Once defined, the primary corporate identity cannot be changed.
- The enterprise data in the USB drives might need to be tied on the protected devices based on the Azure information protection client for Windows (Azure RMS) config for encryption.
- Direct access is incompatible with WIP
- The NetworkIsolation Group Policy setting can override the MDM WIP Policy settings.
- If Cortana (Windows 10 virtual assistance) is added as a protected app, it can still cause data leakage.
- WIP works best for one user per device. For multiple user settings, the second user might experience app compatibility issues.
- App installation files downloaded from the enterprise network might not run as expected.
- Folders with client-side caching are not protected with WIP
- Remote Desktop Protocol (RDP) can be used to connect to a WIP-managed device.
- Upload of an enterprise file to a personal location using Microsoft Edge or Internet Explorer is not possible.
- Resilient File System (ReFS) is not supported by WIP.
- Webpages using ActiveX controls are not protected by WIP.
- Folders having the MakeFolderAvailableOfflineDisabled option set to False are not protected by WIP
- Files in Windows directory cannot be encrypted
- Microsoft Office Outlook offline data files are not protected by WIP
- Without MDM enrollment, only enlightened apps can be managed under WIP. Hence, it is recommended to use WIP in combination with Scalefusion MDM.
Scalefusion MDM enables enterprise data encryption and protection by using the combination of access control settings, WIP, and Bitlocker.
Windows Information Protection vs Azure Information Protection (WIP vs AIP)
We have discussed the list of features and security settings for the Windows MDM policy, specifically the Work In Progress (WIP) container. The Azure Information Protection (AIP), previously known as Azure RMS, is also a feature introduced by Windows 10 to prevent corporate data leakage.
But there is a difference between Windows Information Protection and Azure Information Protection.
Azure Information Protection AIP is a cloud-based set of settings that enables IT admins to label, classify and secure documents and messages for on-prem devices that are a part of Office 365 AD.
While the documents and messages can be protected using the Office web and desktop applications on Office 365, the AD RMS helps in securing the documents and messages leveraging the capability of on-premise hardware.
The biggest difference between WIP and AIP is that it cannot solve the data encryption problem of mixed devices or BYOD. In AIP, the entire data set and apps are encrypted whereas in WIP, only the selected apps (enterprise apps) and the data in motion via these are encrypted.
In WIP, the work data is automatically encrypted after defining the profile settings. Also, WIP tags the data based on its source and any data flowing in from the enterprise data sources is encrypted. This enables the employees, who are the device owners to have total control over their personal data such as files and apps.
Another major difference between AIP and WIP is WIP needs an MDM solution for policy defining and works only on Windows 10 Anniversary Edition or later.
Summary
This comprehensive Windows Information Protection guide can help enterprise IT teams leverage the WIP settings for protecting corporate data with ease using Scalefusion MDM.
Scalefusion MDM for Windows 10 has a wide range of security features and access control settings that make working to BYO PCs a breeze for the employees, adding to their productivity while simplifying the management for the IT teams.
FAQs
1. What are the benefits of Microsoft Windows information protection?
Microsoft Windows Information Protection (WIP) provides robust data security by encrypting and classifying sensitive information. It allows organizations to control access to data, prevent data leakage, and ensure compliance with regulations. WIP safeguards confidential data, enhances productivity, and mitigates risks of unauthorized access or data breaches.
2. How do I turn on Windows information protection?
To activate Windows Information Protection, navigate to Settings > Update & Security > Windows Security > Virus & Threat Protection. Click on “Manage settings” under “Virus & threat protection settings” and toggle on “Block suspicious behaviors.”
3. What are the benefits of Windows Information Protection (WIP)?
Windows Information Protection (WIP) offers several benefits, including data protection by encrypting sensitive information, segregation of personal and work data, control over app access to corporate data, and flexible policy enforcement to prevent data leaks, enhancing overall security and compliance measures within organizations.
4. How does WIP work?
Windows Information Protection (WIP) helps safeguard sensitive data by separating personal and corporate information. It classifies and encrypts data based on policy, ensuring only authorized users and apps can access corporate data. It offers seamless protection across devices and integrates with MDM solutions for management.
5. How do I use Windows information protection?
To use Windows Information Protection, first, ensure it’s enabled in your Windows settings. Then, define your organization’s data protection policies. Once configured, WIP automatically applies these policies to safeguard sensitive data on Windows devices, helping prevent data leaks and unauthorized access.


