There was a time when all corporate data remained strictly private and was stored on company-owned PCs and computers located in secure office premises.
Today, however, enterprise mobility has paved the way for remote access. Employees regularly access and store corporate information on their company-issued or BYO devices.

Modern business trends demand powerful security features to ensure data protection even in the most adverse situations.
To address the same, Apple extends a security feature called remote wipe or remote device erase, which allows businesses to remote wipe an iPhone and prevent data breaches and unauthorized access to sensitive information even if their employees’ iOS devices are stolen or lost.
What is Remote Wipe-Off?
Apple allows IT admins to leverage the ‘erase all content and settings’ option with which the corporate data stored on the user device can be remotely wiped off.
This works for both company-issued devices and BYO devices. Users can track their lost phone using Apple’s Lost Mode and further leverage the Find My app to select the device and erase the data on it.
When and Why You Should Use Remote Wipe for iPhone and iPad?
What’s worse than knowing that you are unable to find your iPhone or iPad which contains several confidential corporate files? You instantly think of the worst that can happen. Strangers find your device and leak your valuable data.
Despite having your iPhone and iPad device password-protected, a lost or stolen device is always at risk of a breach. If your employees ever reach you claiming they are unable to locate their iPhones/iPads, you must have an instant quick-fix strategy to ensure your corporate data protection.
Another scenario in which remotely wiping iPhones and iPads proves extremely valuable is when your employees resign or retire from your organization.
Whether an employee is associated with your organization for a year or 25, there’s a considerable amount of corporate data that is at risk of being exposed intentionally or unintentionally after the employee leaves the organization.
Insider data breaches are a real thing. This is why remotely wiping off the corporate data from work apps and folders of your employee BYO iPhones/iPads is a wise thing to do.
How to Remotely Wipe iPhone and iPad?
If your employees’ Apple devices such as iPhones, iPads, or mac devices get lost or stolen, you can easily retrieve their last location by logging into iCloud and signing into Apple’s Find My app.
Apple’s ability to remotely erase the data on iPhone and iPad allows all sensitive information such as banking details and passwords to be deleted from the device.
Here’s a step-by-step process to erase your lost or stolen iOS device:
- Sign in to the Find My app by logging into iCloud.com
- Use the Find My app to identify your lost device and erase the data on it
- If your device is online, the remote erase action initiates after you follow a few simple onscreen instructions
- If your device is offline, the remote erase action will initiate the next time the device comes online
Read more: What is Apple MDM?
Remotely Wiping Data from Your iPhone and iPad with MDM
Apple has several built-in security features, such as mark as lost, find my iPhone, and location tracking, which instantly protect your devices if they are ever lost or stolen. You can also perform a full device factory reset on your iPhone and iPad using powerful iOS MDM solutions like Scalefusion.
All you need to have is a Scalefusion admin account with factory reset privileges and your employee iOS devices enrolled with Scalefusion MDM.
Here’s how Scalefusion MDM helps protect your lost or stolen iOS devices:
- Monitor your iOS devices remotely with GPS-based location tracking.
- Track suspicious activities with Geofence-based alerts.
- Remotely lock devices in case they are reported lost/stolen by your employees.
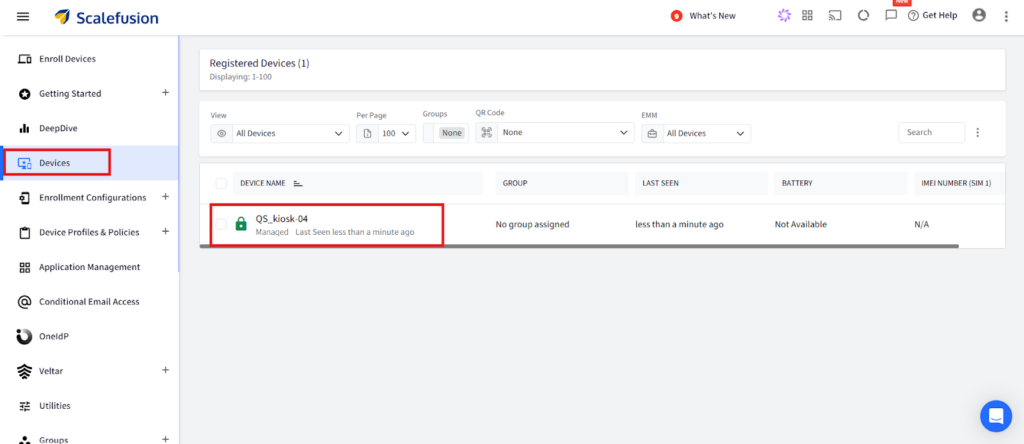
- Locate the device in the Scalefusion dashboard.
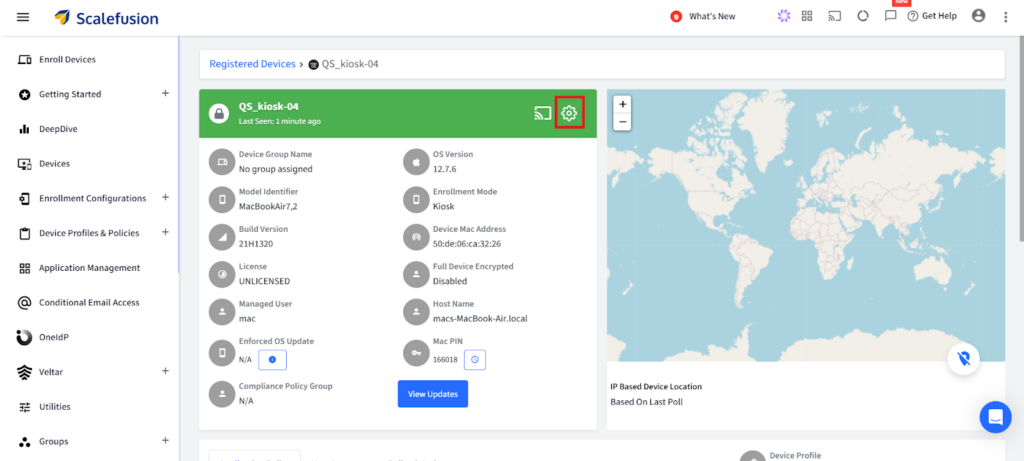
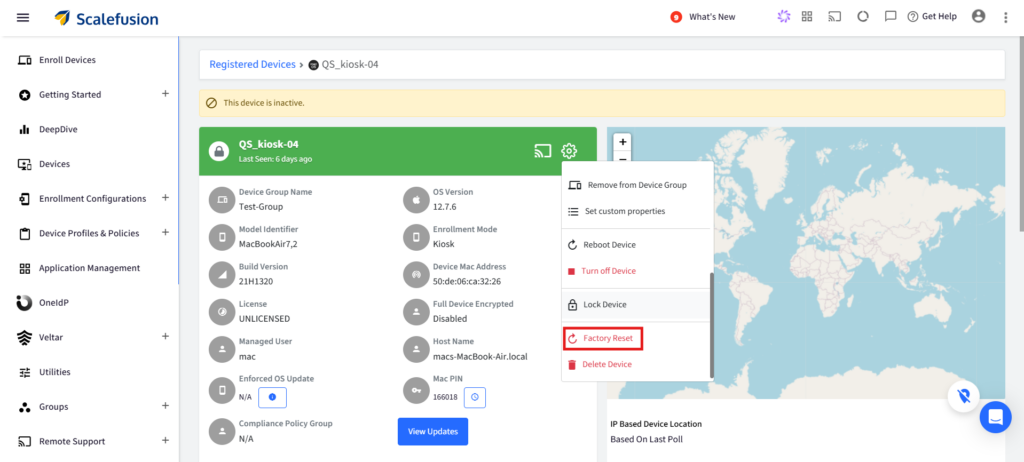
- Click on the gear icon to open the quick settings menu.
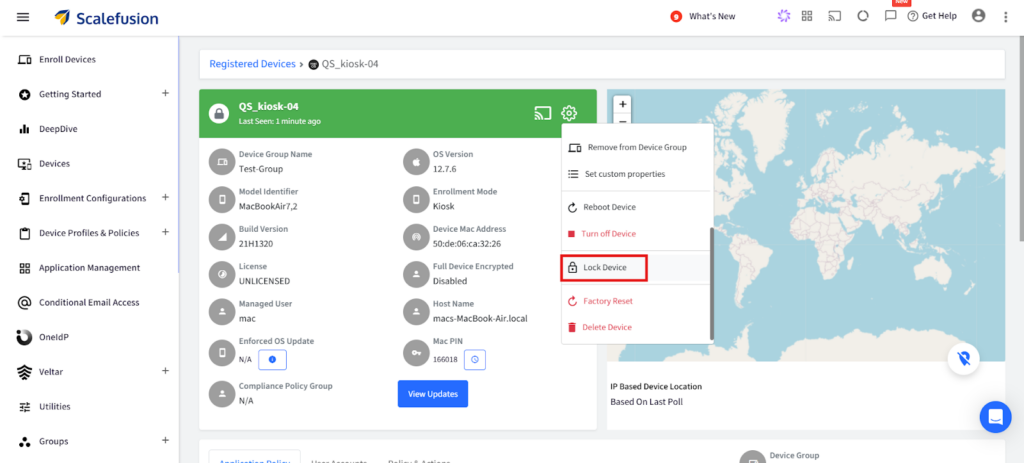
- You now get option to lock the device.
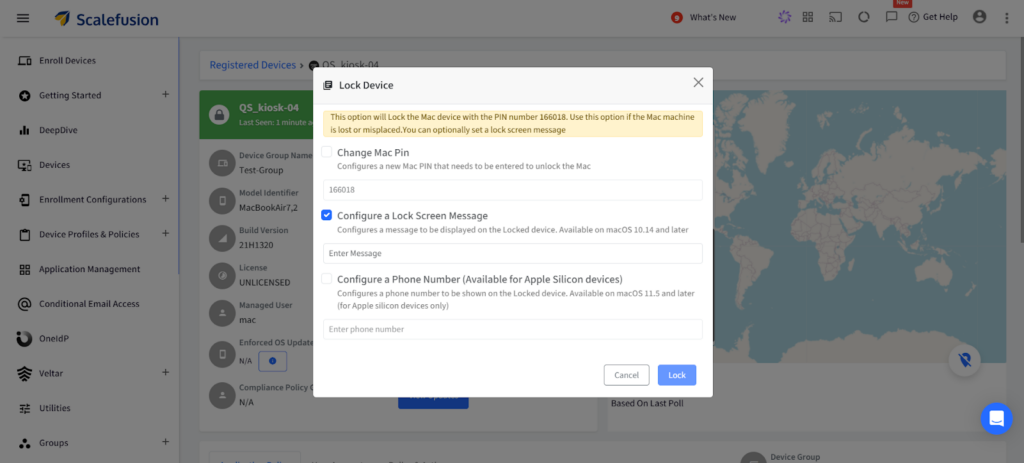
- You can choose to set a Lock screen message to be displayed, add contact details, and put a PIN required to unlock.
4. Remotely factory reset your lost/stolen devices straight from the Scalefusion dashboard.
Closing Lines
There are multiple ways of protecting your iPhone and iPad against unauthorized access. You can leverage Apple’s built-in capabilities, such as Face and Touch ID, or Lost Mode.
Similarly, you can further improve your corporate security by enforcing strong security policies using iOS MDM solution, such as passcode policies, data encryption, and compliance alerts.
In essence, the ability to remotely wipe data off your lost iOS devices is a surefire method to impede misuse of your confidential data.
Explore more about Scalefusion’s Remote Wipe-Off capabilities.
Sign up for a 14-day free trial now.
FAQs
What is MDM and how does it help with remotely wiping iPhone?
MDM stands for Mobile Device Management. It’s a tool that lets IT admins control and secure company-owned iPhones and iPads, including remotely wiping iPhones in case of loss or theft. Think of it as a virtual IT hand reaching into the device.
Can I remotely wipe my personal iPhone or iPad with MDM?
No, MDM remote wipe is typically only for devices enrolled in a company or organization’s MDM system. Your personal device wouldn’t be enrolled in such a system.
What happens when I remote wipe an iPhone or iPad with MDM?
All data and settings on the device are securely erased, making it unusable and protecting sensitive information. It’s like a factory reset, but triggered remotely.
Do I need special access or permissions to use MDM remote wipe?
Yes, only authorized IT admins with MDM access can initiate remote wipe. This ensures it’s used responsibly and only when necessary.
What are some alternatives to MDM remote wipe if I lose my iPhone or iPad?
If your device isn’t MDM-managed, you can try using Apple’s “Find My” app to lock or erase it. Remember, this only works if the device is online.
How to wipe iPhone remotely without iCloud?
MDM solutions like Scalefusion are primarily used by businesses and schools to manage devices. If your iPhone is enrolled in an MDM, the administrator can remotely wipe it, even without iCloud.

