With the ease of accessing data on fingers digitally, comes the risk of it being in the wrong hands. Data is a highly vulnerable asset for anyone, be it an individual or a business, and it needs protection. Without the data loss prevention solutions, it’s just like an open vault in a bank, for anyone to steal and misuse.
Nearly 1 million people’s personal data was leaked due to a system configuration issue and excessive internal access.[1] As data is no longer restricted to hard copies, one wrong click or misstep, whether unintentional or not, can lead to major hazards.
Cybersecurity threats are not industry-specific; from crypto platforms to healthcare and education, all have been hit by them. According to a recent report, about 50 major global companies’ corporate data is being auctioned by a high-profile threat actor, “Zestix [2].”
Data loss prevention (DLP) solution is the answer to all the data security issues. Various businesses and organizations opt for it for better control over their data being shared and effective compliance.
But first, let’s learn what a DLP solution is and some of the best DLP solutions out there.
What is a DLP solution?
A DLP solution is a cybersecurity strategy to prevent data loss and misuse. Sensitive data is not just network-centric; different endpoints such as mobile phones, laptops, desktops, and even cloud applications all open a lead for breach. To identify, monitor, and protect this sensitive data in organizations, it’s important to use DLP solutions.
The loss of data might be intentional or an accident, but it can harm both the individual and the business.
Significance of DLP solutions
Data is more precious than ever, and protecting it has become a necessity. Data breaches can steal your identity, which can later be misused for any kind of activity. As businesses are moving forward with technology and leveraging AI, the stakes of data loss are increasing.
A DLP protects personal identifiable information (PII), intellectual property, and other sensitive data of an organization or its customers. A breach can cause operational failure, financial loss, and a negative effect on reputation. Apart from protecting data, a DLP helps an organization remain compliant with global policies such as GDPR, HIPAA, and PCI DSS, preventing hefty fines.
DLP comes in as a comprehensive solution to prevent data leaks, combat breaches and cybersecurity threats. There are several solutions out there based on endpoints, integrated with other tools, compliance reporting, and so on. Hence, choosing the best DLP solution is crucial.
10 best DLP solutions to solidify your data security
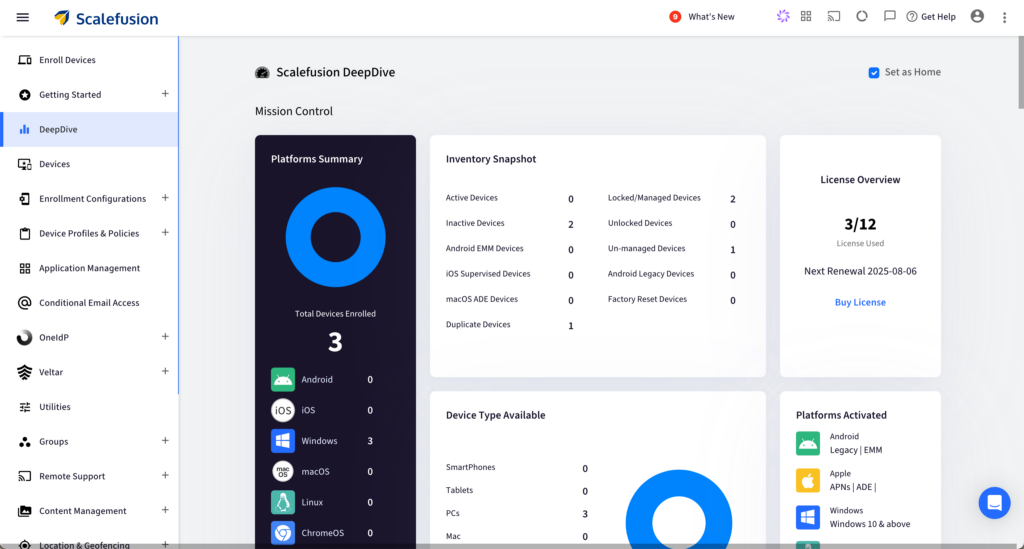
1. Scalefusion Veltar
Scalefusion Veltar is an endpoint-centric data loss prevention (DLP) solution. As different teams work around the world and use various devices, ensuring data security from endpoints becomes a necessity. Veltar helps control how the data is shared and transferred from endpoints, reducing the possibility of a breach.
With Veltar’s endpoint security capabilities integrated directly into Scalefusion UEM, IT teams can enforce policies, manage applications, and ensure compliance across all OS. A single dashboard provides visibility and control over the security posture of all managed devices. This reduces the need to operate another tool for data security and compliance.
Several features, such as web content filtering and automated endpoint compliance, help reduce data exposure risk. On-device policy enforcement makes sure that sensitive data on the device remains protected at all times, keeping unauthorized access, data leaks, and tampering at bay.
Organizations can enforce various compliance policies on how the data should be shared through various forms, such as email, web, USB, or cloud.
Key features:
1. Access level configuration: An access policy can be set to read and write, read-only, or deny all access. This feature ensures that a non-authorized person cannot make changes to the sensitive data.
2. Conditional access restrictions: Set the parameters to configure access restrictions based on different conditions, such as IP address, device timezone, day, date, start, and end time.
3. Encryption enforcement: Data can only be accessed from an encrypted and secure device, reducing the chances of being exposed to a compromised device or network.
4. Device type filtering: For better security, restrict access by the type of device allowed to connect, such as USB blocking, SD cards, or external hard drives.
5. Access logging: Veltar captures all the details of device activities for better audits and compliance.
Strengthen Your Data Security with Veltar’s DLP
Prevent data leaks in real time across all endpoints.
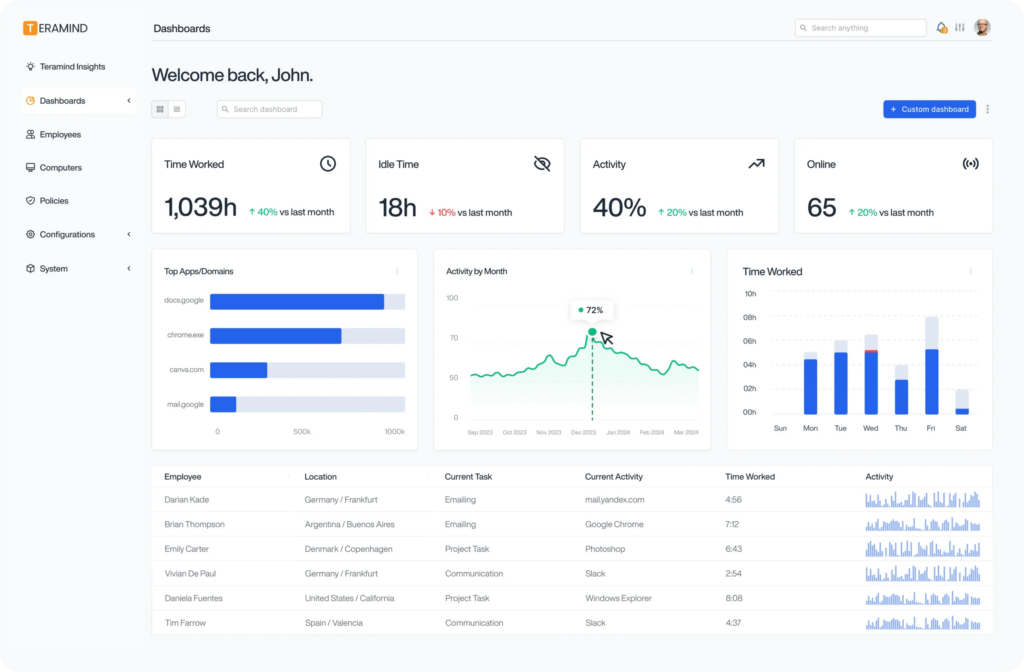
2. Teramind
Teramind’s endpoint data loss prevention is also a user behaviour analytics solution. By using AI-powered analysis and real-time monitoring, it prevents data loss. Automation of these analyses and classifications helps to prevent a gap between.
Key features:
1. Optical character recognition (OCR): OCR is used to search content on screen in any form or unstructured data for compliance audits. The feature also provides a live screen recording of the user events.
2. File share/block: Prevent or block an uncompliant file from being shared in or out of your devices. This feature helps with handling sensitive data files.
3. Email monitoring: This feature helps track inbound and outbound emails for unauthorized file sharing and attachments.
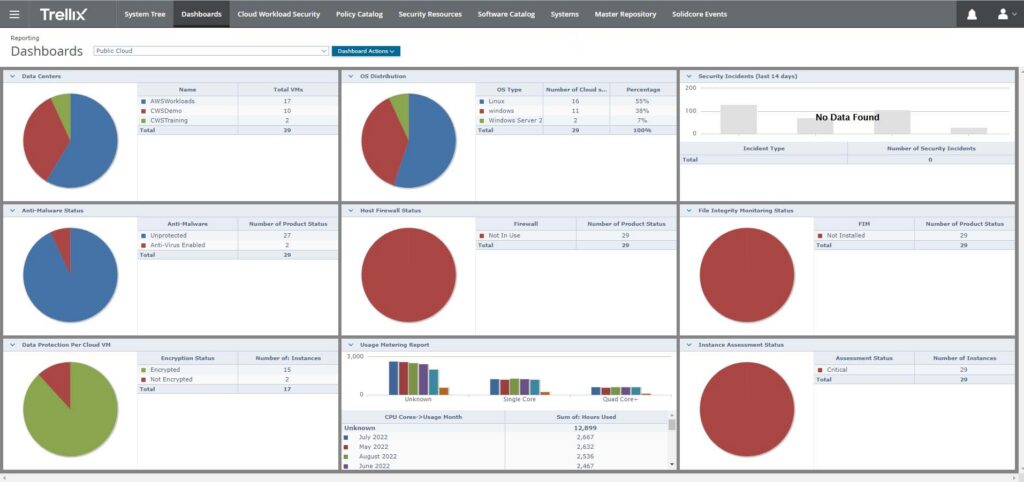
3. Trellix
Trellix Data Loss Prevention (DLP) is an enterprise platform that helps protect data across all endpoints. It prevents data loss at various levels of the network, storage, and cloud services. The solution uses real-time monitoring and policy-based controls to prevent unauthorized data access and sharing.
Key features
1. Centralized monitoring and event tracking: Through a single console, all activities can be monitored in real-time. This feature helps administer policies and ensure compliance.
2. Instant end-user coaching and notifications: Customize notifications for users who try to share unauthorized files without impacting the overall operations.
3. Deploy policies across top threat vectors: Deploy out-of-the-box rules and set parameters for sharing data. Cover all aspects of sharing data locally or on the cloud.
4. Forcepoint
Forcepoint ONE Data Security is a cloud-native DLP solution. With rapid deployment and policy management, it helps safeguard data, prevent breaches, and enforce compliance. It provides real-time risk monitoring across all endpoints, be it cloud apps, emails, or other managed devices.
Key features
1. Risk-Adaptive Protection (RAP): Using several behavior indicators, RAP identifies risks in real-time and risk calculations. With the insights gained, it becomes easy to deploy policy enforcement.
2. Data classification: To eliminate manual errors and improve precision, Forcepoint DLP uses AI Mesh technology and leverages large language models.
3. Predefined compliance policies: Hundreds of predefined templates are provided to maintain and regulate compliance. All policies can be rolled out across all channels, including endpoints, web, email, and cloud applications.
5. Microsoft Purview Data Loss Prevention
Microsoft Purview Data Loss Prevention is a cloud-native data protection solution. It restricts unauthorized sharing, usage, or transfer of sensitive data in devices, apps, and services, including Microsoft 365 Copilot, with a single policy framework. It covers all endpoints and cloud environments such as OneDrive, SharePoint, Exchange, and apps other than the Microsoft cloud.
The Microsoft Purview Information Protection data security solution helps with data classification, sensitive data labelling, and policy-based controls across your digital environment.

Key features:
1. Centralized policy management: Using the Microsoft Purview compliance portal, you can create, manage, and enforce data loss prevention policies.
2. Integration with Microsoft Purview Information Protection: Leverage the classification and labelling capabilities of the information portal that help classify sensitive information and with out-of-the-box policy enforcements.
3. Unified alerting: Track data sharing and send alerts through a single console. This helps in monitoring real-time policy violations and minimizing breaches.
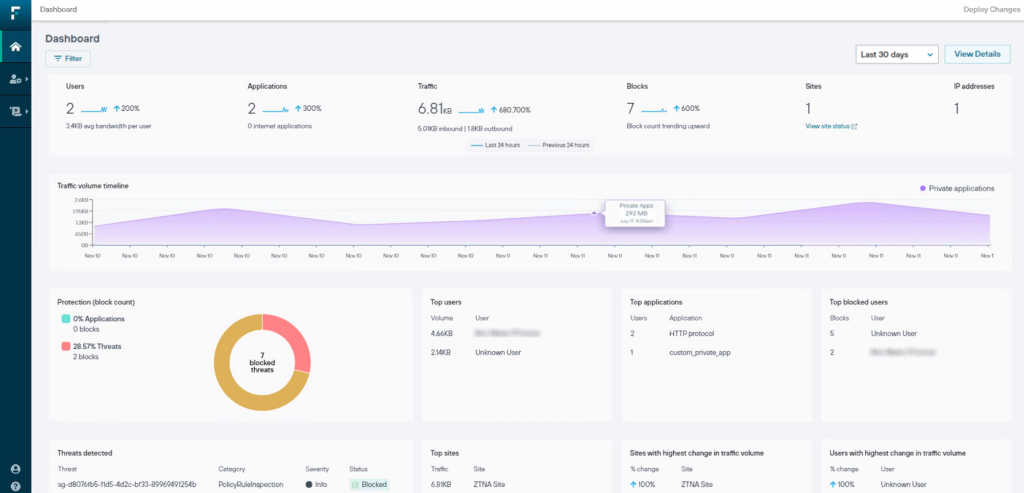
6. Zscaler Data Loss Prevention
Zscaler Data Loss Prevention offers a unified, cloud-native solution that integrates DLP within the Zscaler Zero Trust Exchange platform. It helps secure data across all endpoints, cloud applications, and data in transit. It provides full visibility and control of data from everywhere.
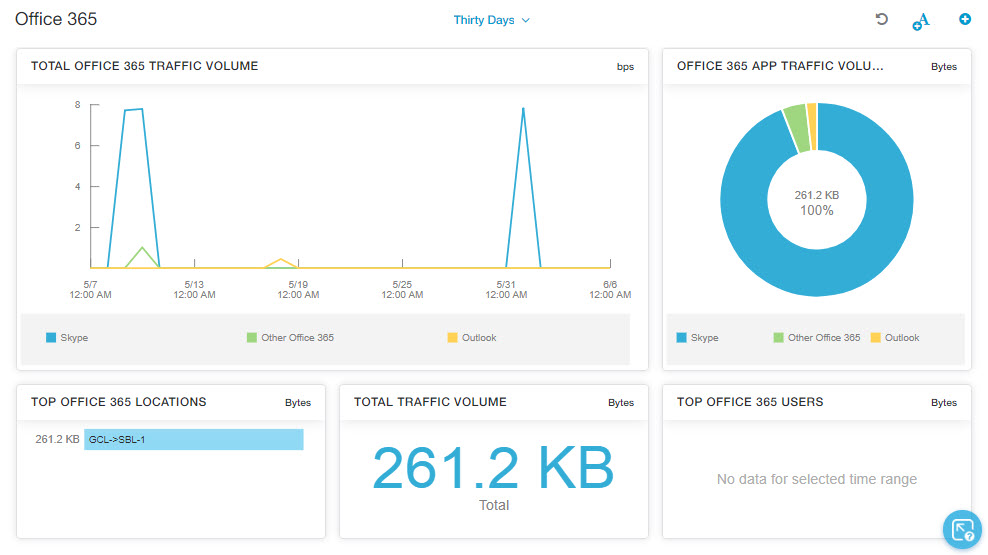
Key features:
1. Endpoint DLP: Secure the data from all endpoints and actions such as USB transfer, printing, and network share with USB blocking software.
2. Workflow automation: Automate incident management and user coaching.
3. Advance classification: Use advanced classification techniques such as exact data match (EDM), indexed document matching (IDM), and OCR. Secure data, documents, and screenshots.
7. Fortra
Fortra is an enterprise software solution that provides comprehensive DLP, from endpoint to cloud. It delivers cloud-powered DLP that discovers, classifies, monitors, and blocks sensitive information. It spans endpoints (Windows, macOS, Linux) and network channels.
The solution works on a granular level and lets you control data sharing and loss protection at the endpoint level. It lets you monitor user activities such as applications used, data transfer, and files created and uploaded.
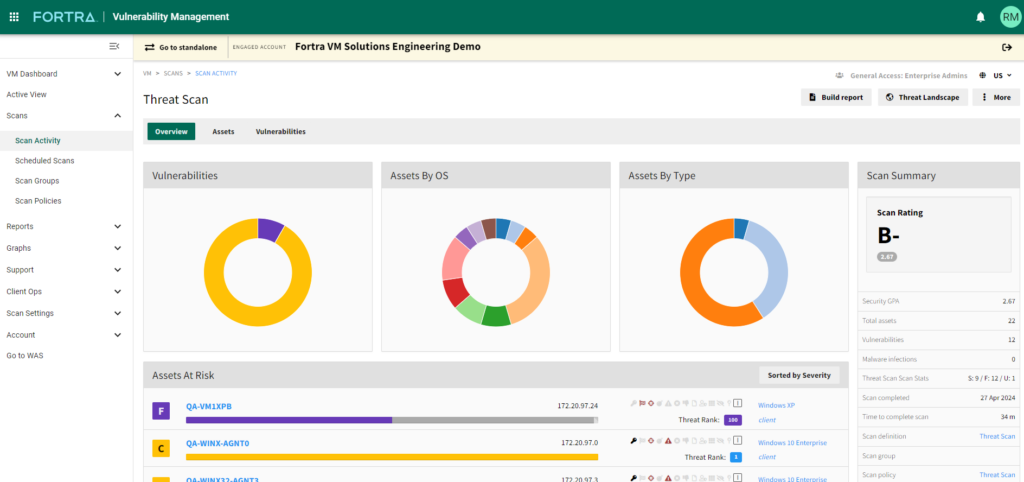
Key features:
1. Analytics and reporting: Monitor systems and data-triggered events. You can also set alarms for high-fidelity events that may need additional actions.
2. Drag-and-drop incident management: To create a new event, artifact, or alarm, you can use the drag-and-drop feature for ease.
3. Remediation in real-time: Monitor the activities in real-time and enforce data protection policies. Automate various processes such as blacklisting, scanning, and warning on launch.
8. Radiant Security
It is an AI-driven, DLP + SOC automation platform. It uses a combination of behavioral analysis, alert triage, and automated policy enforcement. It uses behavioral AI to determine the real threats, reducing manual triage and alert fatigue. It modernizes DLP operations by triaging every alert and orchestrating an integrated response.
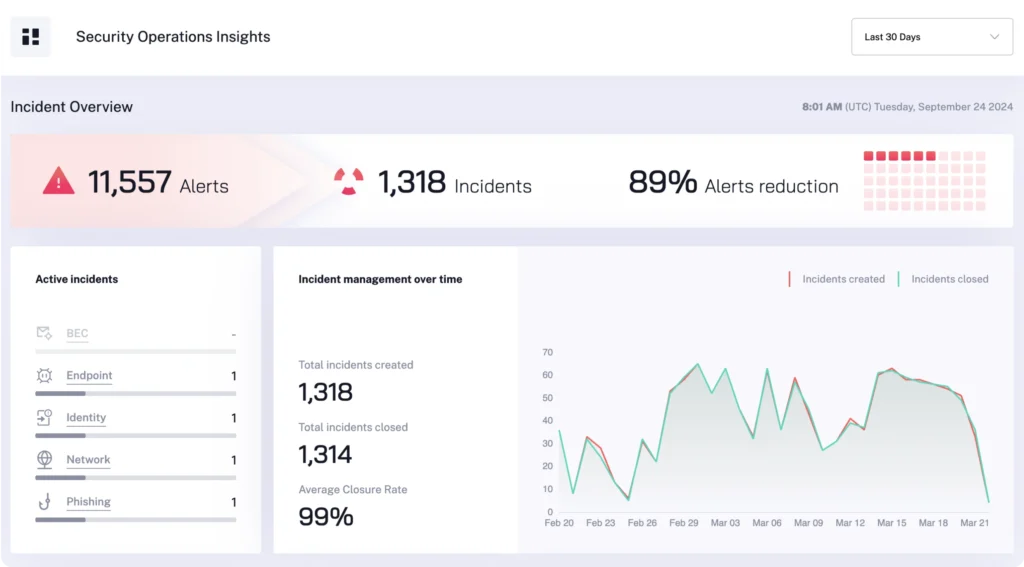
Key features:
1. Agentic AI triage: Leverage AI that builds and uses triage logic for every alert, including the full context at every step taken.
2. Integrated response: To resolve escalated incidents, use the auto-generated response. It helps contain the threats and respond in record time.
3. Log management: Monitor and respond to user activity with built-in log management. This reduces the log storage compression costs.
9. Mimecast Incydr
Mimecast Incyder helps detect and stop data loss from insiders. It is a cloud-native data protection and insider risk and threat management solution. It prevents and responds to risky user behavior in time. It emphasizes data context (e.g., file sensitivity) and user behavior (e.g., role). The solution protects critical data from being exposed, lost, leaked, or stolen while speeding up incident response time.
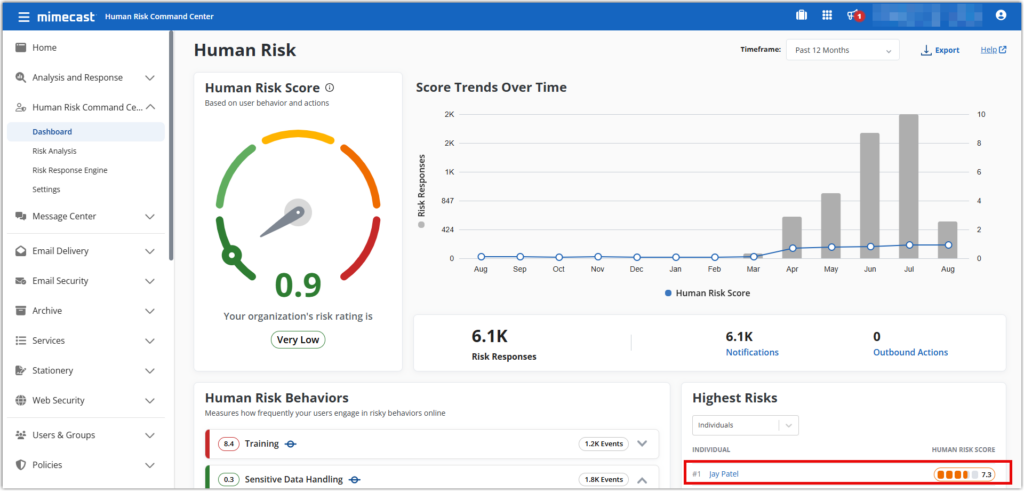
Key features:
1. Eliminate blind spots: Mimecast Incyder prioritizes risk detection and eliminates blind spots using its PRISM (Proactive Risk Identification & Severity Model) system for both known and unknown data risks.
2. Overall coverage: Mimecast Incyder protects and stops data theft and leaks from endpoints, including browsers and cloud applications. It helps protect sensitive data and source code.
3. Automated response control: Mimecast Incydr offers native, customizable response controls to mitigate insider data risks, ranging from accidental mistakes to malicious threats, using automated actions.
10. Proofpoint Enterprise DLP
Proofpoint Enterprise DLP is a people-centric solution protecting endpoints, cloud applications, and emails. It inspects content using behavior analytics and threat intelligence. It understands people’s patterns with data and how they share it by detecting data movement and correlating with events such as compromised accounts and phishing attacks.
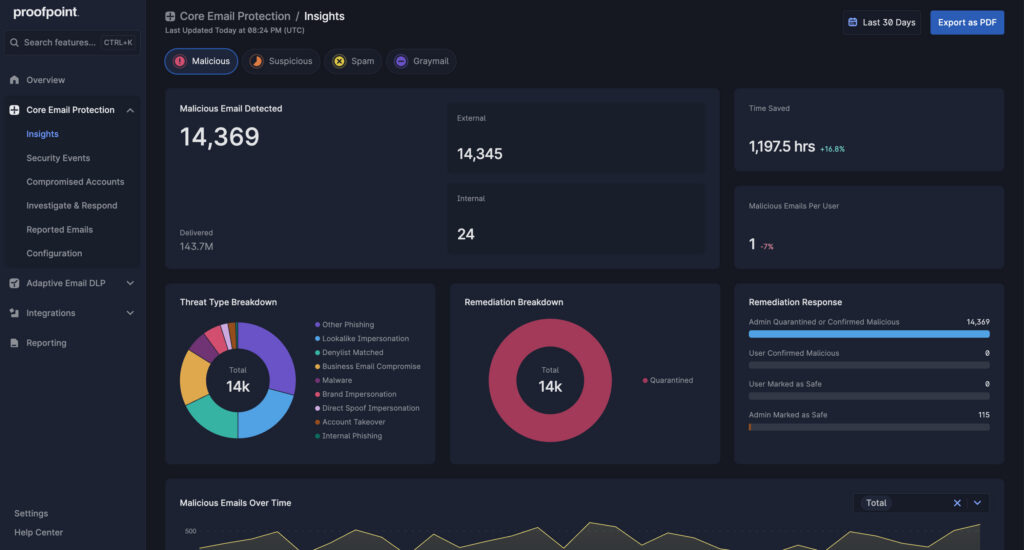
Key features:
1. Insight into user activity: Detect user activities from managed to unmanaged endpoints and the cloud, which also includes data within the images. You can detect changes to file extensions, application usage, and file copies.
2. Unified console: View all user activities at a glance with the search and filtering feature. Search for data exfiltration and risky activities.
3. Cloud-native architecture: Scale the DLP solution to thousands of users per tenant and implement it with your cloud security infrastructure. Its lightweight user-mode endpoint agent doesn’t conflict with other security tools, making the integrations smooth.
How to choose the best DLP solution?
Selecting the right DLP solution is more than comparing feature lists. It requires meeting your organization’s standards, workflow intensity, and most importantly, sensitive data protection needs.
- Unified visibility: The first priority should be visibility, knowing exactly where the sensitive data resides across all endpoints. A reliable DLP solution should continuously monitor all endpoints in real-time, providing centralized visibility and management of how the data is shared, accessed, and stored.
- Intelligent filtering and monitoring: Look for an advanced content filtering feature that can detect sensitive keywords, block suspicious links and filter URLs, and prevent risky data transfer.
- Identity access control: The right DLP should allow role-based access control to eliminate unauthorized access to sensitive data.
- Automated policy enforcement: Policies must stay up-to-date. Ensure automated policy enforcement to prevent security gaps.
- Seamless integration: A highly capable DLP solution should integrate smoothly with other identity providers, productivity tools, and third-party applications.
Find the best DLP solution for your organization: Final Thoughts
Finding the best DLP solution for your organization means choosing a platform that provides complete endpoint visibility, intelligent control, and effective policy enforcement without disrupting your workflow.
Scalefusion Veltar brings all of this together under one unified solution. It provides advanced data monitoring, granular policy controls, cross-platform support, and centralized analytics. It empowers organizations to prevent data loss confidently and efficiently across all endpoints.
Safeguard sensitive enterprise data on every endpoint with Scalefusion Veltar.
Sign up for a 14-day free trial now.
References:
FAQs
1. How to choose the best DLP solution?
To choose the best DLP solution, assess where your sensitive data resides and how it moves across all endpoints. Solutions like Scalefusion Veltar strengthen protection with endpoint-centric enforcement, secure web gateway, and a compliance solution.
2. Is DLP a firewall?
No, DLP is not a firewall. It focuses on preventing sensitive data from being lost and misused. The best DLP solution monitors and controls data movement across endpoints, cloud apps, and email, beyond basic network filtering.
3. How difficult is it to deploy and maintain a DLP solution?
Deployment complexity depends on architecture, but modern DLP solutions offer a centralized management dashboard. Endpoint-focused platforms like Veltar simplify rollout without heavy overload.
4. Is DLP part of endpoint detection and response (EDR)?
DLP and EDR serve different purposes. EDR detects and responds to endpoint threats, while DLP prevents sensitive data loss. The top DLP solutions complement EDR by adding data visibility and policy enforcement.
5. Which DLP solutions are considered ideal for small and large enterprises?
The best DLP solutions for small businesses prioritize ease of deployment and simplified management. Large enterprises typically require advanced classification, compliance controls, and integration. Solutions like Veltar offer simplified endpoint visibility with its intuitive dashboard, suitable for both small and large enterprises.

